As a sysadmin, when you are working on a remote system or server, multiple users might be accessing the same system via SSH simultaneously.
Active users can gently disconnect from the server by issuing the “exit” command in the terminal once they are done with their work.
However, some careless users fail to logout and leave the session running in the background, which will logout the user only if you configured SSH to automatically kick out the user after a certain amount of idle time or the user logs out manually.
In this quick tutorial, you will learn how to kick out SSH-connected users from the target system from your end as a sysadmin.
Tutorial Details
| Description | Logout the SSH Users from the System |
| Difficulty Level | Low |
| Root or Sudo Privileges | Yes |
| OS Compatibility | Ubuntu, Manjaro, Fedora, etc. |
| Prerequisites | who, kill, killall |
| Internet Required | No |
Finding All the Logged-In Users in the Linux System
The first thing you need to do is list all the logged-in users connected to the target machine via SSH; that can be achieved using the multiple command-line tool.
For now, I will use the who command along with the “-u” flag to list all the logged-in users along with their process ID.
$ who -uOutput:
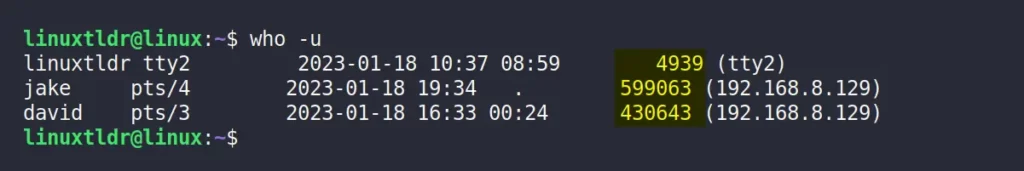
From the above picture, it’s clear that the three users with account names linuxtldr (myself), jake, and david are connected to the target machine.
Next to each user’s account name, you can find their account information, like their TTY, date and time, process ID, and IP address.
Currently, we are only interested in users process ID to kick them out of the system (the primary objective of this article), which you will learn in the next section.
Kick Out the SSH Users from the Linux System
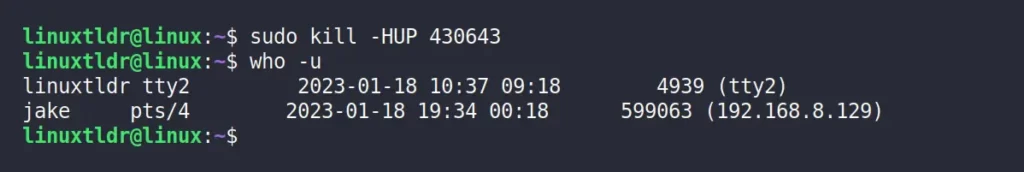
As you now have a list of all the logged-in users connected to the target machine along with their process ID, you can easily kick them out of the system using the kill command.
For example, I want to kick the “david” user from the system, so I will use his “430643” PID as an argument to the kill command with the “-HUP” option.
Operation not permitted” message.$ sudo kill -HUP 430643The above command will send a “SIGHUP” signal to gently disconnect all the processes in the session from the controlling terminal.
Forcefully Throw the User from the Linux System
Sometimes the “SIGHUP” signal (responsible for gently disconnecting users) might not do the trick, especially when the SSH session becomes unresponsive.
In that case, you can aggressively kick out the users from the system by sending the “SIGKILL” signal.
$ sudo kill -SIGKILL 430643
#OR
$ sudo kill -9 430643Send a Message to the Users Before Terminating the Session
Sometimes you want to intentionally terminate the user session for various reasons, and in that situation, it is quite possible that the user is working on something and terminating the session will lead to data loss.
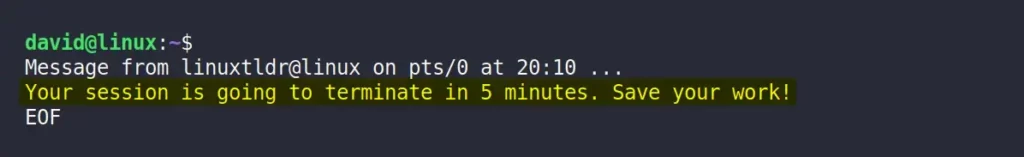
However, you can send them a relevant message before terminating the session using the write command.
$ echo "Your session is going to terminate in 5 minutes. Save your work!" | write david pts/3The following is an example of a target user’s terminal screen.
How to Terminate All the User Active Sessions from the Linux System
It’s entirely possible that the target machine is being operated by the same user from two different SSH sessions, as shown.
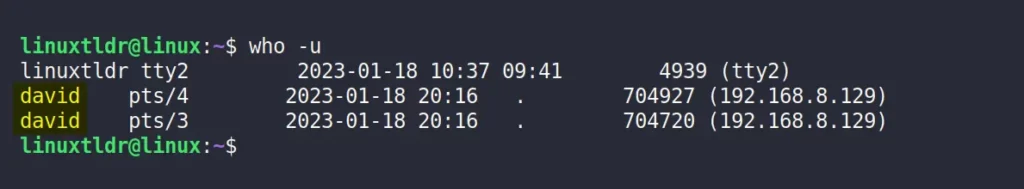
As you can see from the above picture, the “david” user is logged into the target machine with two different SSH sessions, giving him two different process IDs.
Now, one way to kick him out of the target machine is by specifying each session PID as an argument to the kill command (ineffective).
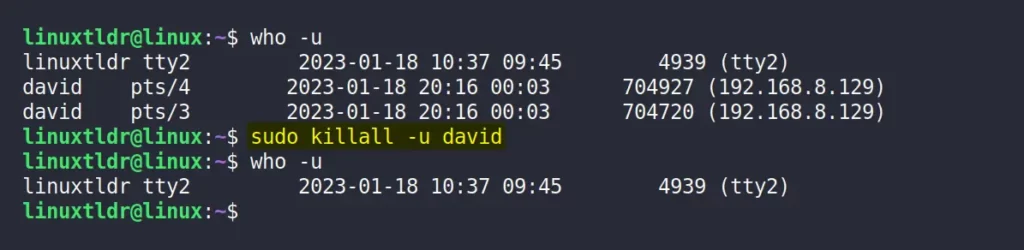
Or, you can specify the user account (or login) name as an argument to the killall command with the “-u” option to terminate all the active sessions of the referenced user.
$ sudo killall -u davidOutput:
And here comes the end of this article.
I hope this article will help you achieve this task; however, if you have any questions or queries related to this topic, then feel free to ask them in the comment section.
Till then, peace!