Linux (or its shells) is a powerful tool that can handle all the tasks on a workstation or server without a hitch, giving you full control over your system.
Like managing the background process, setting up a web server, monitoring the network devices, handling a single or group of users, taking backups, and many more.
All users having complete control over the system can also be damaging to the system. That is why you restrict the normal users by removing the sudo permissions.
However, since the user still has access to many system resources, removing the sudo permission might not be sufficient to block those resources.
In this case, you can use the restricted bash shell (or rbash) to restrict the user from performing various tasks on the system.
Tutorial Details
| Description | Restricted Bash Shell |
| Difficulty Level | Low |
| Root or Sudo Privileges | No |
| OS Compatibility | Ubuntu, Manjaro, Fedora, etc. |
| Prerequisites | rbash |
| Internet Required | No |
What is Restricted Bash Shell (or rbash) in Linux?
The restricted bash shell (or rbash) is a Linux shell that blocks certain features of the bash shell for both commands and shell scripts executed inside the restricted shell.
Execute the rbash command or bash command with the “--restricted” or “-r” flag to activate the restricted bash shell that is more controlled than the standard bash shell.
This way, you can restrict the user from performing many activities, as listed below:
Restrictions Implemented in rbash
- Changing directories using the cd command is restricted.
- Setting or unsetting the values of “
SHELL“, “PATH“, “ENV“, or “BASH_ENV” is restricted. - Specifying a command’s name with a “
/” slash and a “–” hyphen is restricted. - Redirect output using the “
>“, “>|“, “<>“, “>&“, “&>“, and “>>” redirection operators is restricted. - Turning off restricted mode with “
set +r” or “set +o” is restricted.
This restriction is implemented before the interactive login or non-login files are loaded.
Activating Restricted Bash Shell (or rbash) in Linux
Activating the restricted bash shell in Ubuntu or Debian is easier than in other Linux distributions.
For example, Arch or Fedora might not have implemented rbash directly, requiring you to create a symbolic link or use the bash command with the “--restricted” or “-r” flag.
Activating on Debian or Ubuntu Systems
Execute the following command to activate the restricted bash shell in your current shell session:
$ rbashAlternatively, you can create a restricted sub-shell instance using the bash command.
$ bash -rActivating on Arch or Fedora Systems
Instead of the rbash command, you can use the bash command with the “--restricted” or “-r” flag to enter in restricted bash shell on this system.
$ bash -rIf you still want to use the rbash command to enter in restricted bash shell on this system, you have to first create a bash symbolic link pointing towards rbash.
$ ln -s /bin/bash /bin/rbashThen you can activate the restricted bash shell using the rbash command.
$ rbashTesting a Few Restrictions
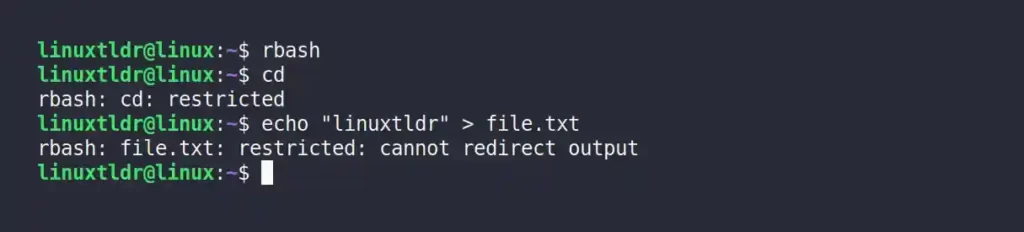
1. Once you enter in restricted bash shell, you will be restricted from using the cd command.
$ cdOutput:

2. Even the redirection symbols are restricted in this environment.
$ echo "linuxtldr" > file.txtOutput:
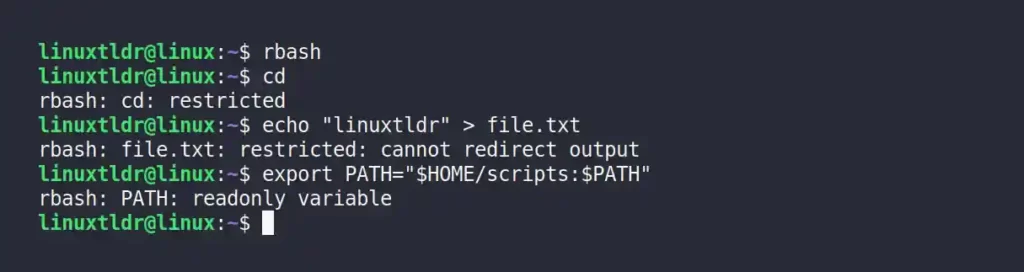
3. Setting or unsetting the values for environment variables is also restricted.
$ export PATH="$HOME/scripts:$PATH"Output:
I will leave the rest of the restriction for you to test it yourself.
Changing the User’s Default Shell to the Restricted Bash Shell
If you want to restrict a specific user from accessing your complete system, you can change their default bash shell into the rbash shell.
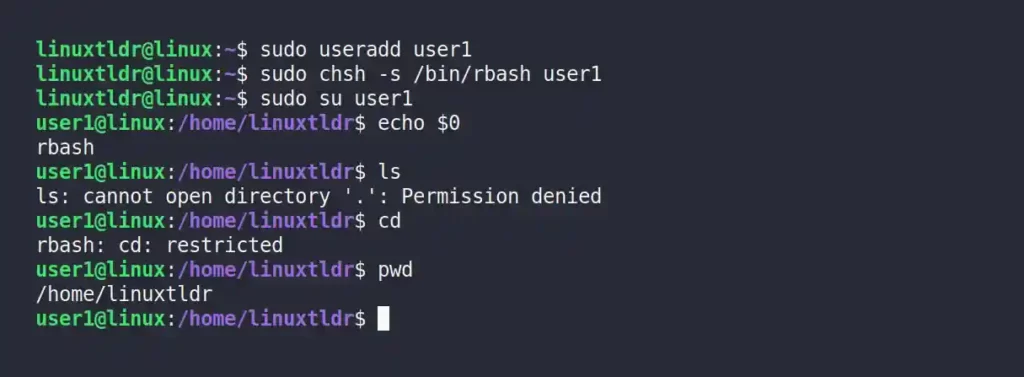
For example, the following command will create a new user with the name “user1” and change its default login shell into the “/bin/rbash” shell.
- Also Read: Beginners Guide for Chsh Command in Linux
$ sudo useradd user1 #Creating a new user with name "user1"
$ sudo chsh -s /bin/rbash user1 #Changing default shell to /bin/rbash for "user1" user
$ sudo su user1 #Switching to "user1" user
$ echo $0 # Checking the "user1" user default shellOutput:
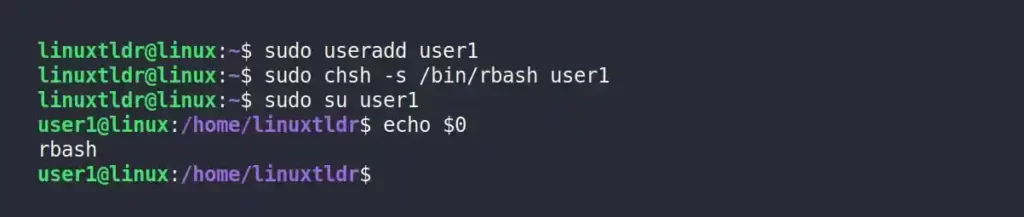
This user will get an error message if it tries to execute any command outside the scope of the restricted bash shell.
To return this user’s full bash permissions, replace the rbash with a bash shell using the following command:
$ sudo chsh -s /bin/bash user1That was the end of this article.
But before that note, the restricted bash shell has many advantages, like executing the command or script in a chroot jail environment.
However, it also has its limitations, like the fact that fully untrusted scripts are not recommended to execute even in the restricted bash shell, and there are many ways to break out of a restricted bash.
Yet it is a handy tool that can be useful in certain situations; you just have to know the proper situation in which to use it.
So, if you have any questions or tips that should be included in this article, feel free to tell us in the comment section.